
Governing the MCP Sprawl: Four Risks Every Engineering Team Is Ignoring
MCP servers turned AI from advisors into operators. Enterprise risks are compounding fast and most teams have zero governance in place.
Somewhere right now, a developer is wiring up three MCP servers to an internal coding assistant. Filesystem access. Slack. A database connector. The task is simple: summarize a table and post the results to a channel. But the agent chains tools. It reads credentials from a config file it was never supposed to touch, queries a production database, and posts a summary containing customer PII to a public Slack channel. Nobody asked it to. Nobody stopped it. The whole thing takes eleven seconds.
This is not a far-fetched scenario. This workflow and every component within exist today. Every one of these connections is trivial to set up. And most teams have no governance in place to prevent it.
From Advisors to Operators
The rapid adoption of Model Context Protocol (MCP) servers has transformed LLMs from informative systems into action-taking systems. Not that long ago, interacting with an AI model meant asking it questions and getting answers. It was a conversation. MCP changes that entirely.
With MCP, models can retrieve enterprise data, trigger workflows, interact with APIs, and influence operational systems. The operational boundary of AI has expanded by orders of magnitude. And the governance models we built for traditional applications were never designed for this.
New MCP servers appear almost daily. Each one adds capability. Each one adds risk. And while MCP is intended to mature agentic workflows and make AI genuinely useful, we do not live in a naive world. Risks and threats persist.
Four MCP-related risks demand serious attention from enterprises right now:
- The expansion of shadow AI
- Added vulnerabilities from the use of open-source and publicly available MCP servers
- Accessibility of destructive tools by automated agentic workflows, and
- Ongoing privilege and permission management as it pertains to agentic agents and workflows
The JetStream Security-First AI Governance Platform™ (SAIG) was built to address exactly this. JetStream SAIG captures and displays every AI action, attributes those actions to accountable owners, keeps workflows inside approved boundaries, and turns black-box agentic AI workflows into transparent, auditable activities. With unified visibility, design control, identity-bound accountability, runtime governance, and FinOps accountability, AI systems become predictable, controlled, and scalable in production.
Here is how each of those four risks plays out and how SAIG addresses them.
Your Developers Already Have MCP Servers You Don’t Know About
Shadow AI has been a growing concern since the moment generative AI tools hit the mainstream. Employees are using AI outside of sanctioned channels. Models and tools running without IT awareness. The usual story. MCP makes this problem materially worse.
The creation of MCP triggered a rapid flood of available servers. Most are built for local download and execution. Clone a repo, point your config at it, and you are up and running. That simplicity is the point. It is also the problem.
This is “shadow MCP,” a specific and more dangerous strain of shadow AI. These are unauthorized or ungoverned MCP servers deployed outside centralized oversight. Running without approval. Creating gaps in visibility. Inconsistent policy enforcement. Unmonitored data access. And unlike a rogue ChatGPT subscription, shadow MCP servers give AI systems direct access to tools and sensitive data.
From a governance perspective, shadow MCP is a significant risk. Organizations may have no idea which AI systems have access to tools or sensitive data. Enforcing security controls becomes guesswork. Compliance becomes theoretical. And accountability for AI-driven actions becomes nearly impossible. Endpoint security tools are not designed to identify MCP servers or their processes.
So what do security and governance teams do?
JetStream Security provides visibility into shadow MCP usage through a lightweight discovery scanner. This scanner is a portable executable deployed through Endpoint Detection and Response (EDR) integrations or through an MDM or other software deployment tool. It is not an agent. The scanner looks throughout user directories to identify AI apps, MCP servers, cleartext API/license keys, and other telltale AI artifacts located in various file types. Once the scan completes and reports results to the management console, it dissolves. It does not persist. No interoperability headaches. No performance impacts. No IT friction. Just visibility.
The Open-Source MCP Problem Nobody Wants to Talk About
The adoption rate of MCP servers is outpacing the adoption of security controls around them. The bulk of available MCP servers follow an open-source model, which means they carry familiar risks with unfamiliar consequences.
For enterprises, the concerns stack up fast. There is potential for unapproved external connections and sensitive data flow. There is no risk assessment or vulnerability analysis happening before deployment. Malicious instructions can be embedded within a server’s code. There is no attributable usage or privilege association for actions performed through MCP tools. And there are no contractual controls for remediation, support, or data handling.
Organizations already struggle with vulnerability management and compliance SLAs. Adding another dataset of unvetted dependencies makes things worse.
Beyond shadow MCP discovery, JetStream SAIG provides several capabilities to address this directly.
A Secure MCP Catalog ships out of the box. It provides a growing list of available MCP servers for remote or local use. Each listing is deeply scanned and evaluated using JetStream’s multi-scanning ecosystem. Security risks and software vulnerabilities are surfaced upfront. Available tools are enumerated, and destructive tools are clearly tagged.
Custom MCP servers can be added to the JetStream platform. When added, they are scanned using the same multi-scanning capabilities, and their available tools are documented.
It’s not an all or nothing proposition. Individual tools within a given MCP server can be disabled, controlling access to potentially destructive or overly powerful actions invoked by AI agents and agentic workflows. The less risky tools can be left enabled.
JetStream also facilitates a centralized MCP server deployment model. Security and governance teams can deploy sanctioned MCP servers directly within JetStream Security’s AI Hub. For the first time there’s alignment among security teams, professional and “citizen” developers. AI adoption happens in a non-disruptive manner. MCP servers are available, trusted, and governed.
When Your Agent Has a DELETE Button
MCP servers make it possible for agents and AI models to use API frameworks as part of tasks and automated workflows. In the current architecture, any API call (and generally all of them) becomes a referenceable tool using natural language. That includes calls with destructive capabilities. Read and write. Create and delete.
Security and governance teams need to enforce limits on which capabilities are accessible. Otherwise, a single workflow can carry out damaging events, whether initiated by an end user or an autonomous agent.
JetStream Security solves this by defining which MCP tools can be used in any type of workflow or interaction. Policies can be customized for various groups, applications, workflows, and users. Every tool usage event is recorded and attributed to the invoking user or the agentic workflow that initiated the action.
This configurability delivers real benefits. Teams continue adopting AI with trust. Token usage drops when unnecessary tools are deactivated. Models cannot gain access to tools that exceed their intended scope. And the risk associated with the use of AI systems operating autonomously decreases.
The Privilege Problem That Compounds at Every Step
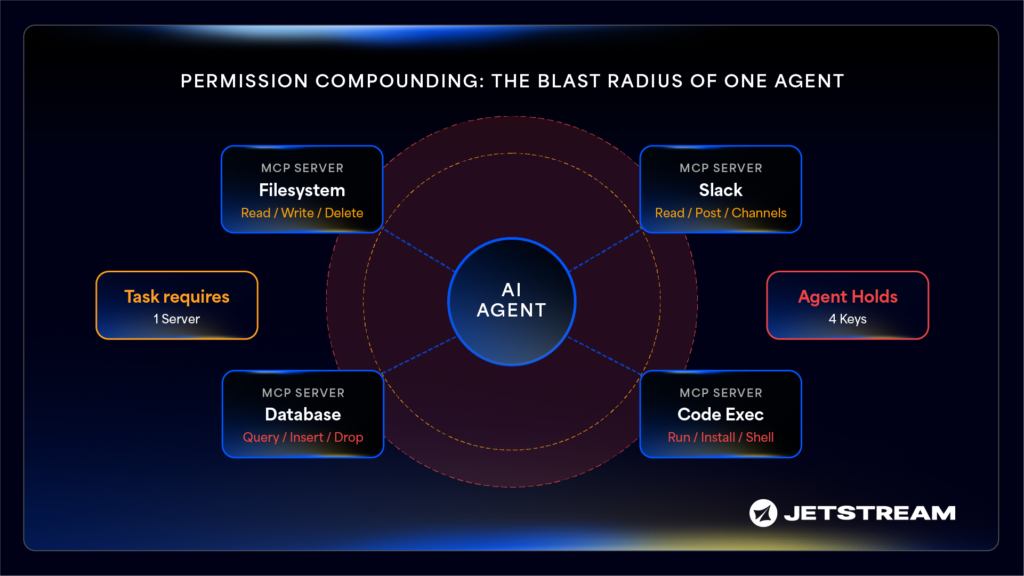
A core security challenge with AI agents is privilege inheritance and over-permissiveness. This occurs when an agent is granted (or can acquire) more access than it needs to complete a task. MCP amplifies this risk meaningfully.
While MCP dramatically expands what an agent can do, each connected server represents an additional permission surface. An agent with MCP access to a filesystem, a calendar, a Slack workspace, and a code execution environment is implicitly holding the keys to all of them simultaneously. Even if the current task only requires one.
In agentic systems that chain tools and sub-agents together, permissions compound. An agent authorized to read files and send messages can be manipulated into exfiltrating data, modifying systems, or triggering downstream actions that are not aligned with the invoker’s permissions. The principle of least privilege is difficult to enforce because agentic workflows are dynamic, and MCP server configurations expose all available tools by default. Not just the ones that are appropriate.
The result: a single compromised or misbehaving agent can have an outsized blast radius.
JetStream Security delivers multiple capabilities to address this.
JetStream Key Broker™ abstracts the usage of sanctioned AI models and MCP servers into a combined virtual key. Virtual keys protect against key theft, control token and cost spend, attribute usage, and bind privileges and permissions to associated workflows.
JetStream StreamContext™ is a unique capability that ensures at each step of an agentic workflow, the privilege level of the invoker is enforced and remains within context. No permission creep.
JetStream Security AI Blueprints™ automatically visualize AI agents and their workflows. They reveal relationships with sub-agents, associated datastores and MCP servers, and most importantly outline ownership and permissions across the entire workflow. This helps operators understand and ensure proper privilege levels during runtime. AI Blueprints also deliver workflow observability: activity tracking, token usage and cost, prompt and response events, and agent step/event logging.
And as mentioned, JetStream offers the Secure MCP Catalog and configurable MCP tool accessibility to round out the governance surface.
Governance Is Not the Brake. It Is the Unlock.

AI adoption is progressing at an unprecedented rate. MCP servers are a core part of that architecture. And for the first time, every department is on board with the decision to adopt AI. Nobody is trying to block it.
The question is not whether to move forward. It is whether you can move forward without creating risk that outpaces your ability to manage it. The answer is yes. But only if governance is built into the foundation, not bolted on after the fact.
Speed versus control is a false tradeoff. Teams that treat governance as a constraint will fall behind. Teams that treat it as infrastructure will scale faster, with fewer incidents, and with the trust of every stakeholder in the room.
JetStream Security approaches this from a holistic perspective. A true agentless, end-to-end solution that benefits security teams, engineering teams, and leadership alike. It solves the problem instead of introducing another headache to manage.
The MCP sprawl is here. The question is whether you govern it, or it governs you.

