The Security Agent Deployment Trap: Why Enterprise AI Governance Doesn’t Need Another Endpoint Agent

Executive Summary
The average large enterprise runs 43 cybersecurity tools, and the majority require a persistent software agent on every managed endpoint. EPP, EDR, DLP, UEBA, MDR, PAM, vulnerability scanners, and patch management platforms each install a dedicated background process that starts at boot and never stops. The compounding cost is not hypothetical: half of every IT work week is now consumed by endpoint security deployment and management alone, 52% of executives name complexity as their top impediment to security operations, and 63% of firms that increased security budgets in 2024 saw no meaningful improvement. This is the condition known as agent sprawl, and it is the operational context into which enterprises are now being asked to deploy AI governance. It carries documented costs in system performance, operational complexity, and security effectiveness.
Security team burnout is a key concern tied directly to this multi-tool complexity, which compounds a pre-existing skills shortage. The most-requested feature among enterprise security buyers surveyed in 2025 was a unified dashboard across endpoints, servers, and cloud workloads, reflecting the daily pain of operating in fragmented, multi-agent environments. (Gartner – Top Trends in Cybersecurity for 2025)
Key Statistics
50
50 %
On average, almost 50% of IT respondents’ work week is dedicated to endpoint security, management, and deployment. (Forrester – “How AI, Web, And Cloud Will Drive The Transformation Of End-User Computing”)
52
52 %
Of executives say complexity is the biggest impediment to security operations. (IBM – Capturing the cybersecurity dividend)
57
57 %
Of CISOs said consolidating multiple security technologies on a single platform or interface would decrease their work-related stress levels. (Cynet – “Implications of Stress on CISOs”
81
81 %
Of respondents said adopting web-based applications is a part of their organization’s digital transformation goals. (Forrester – “How AI, Web, And Cloud Will Drive The Transformation Of End-User Computing”)
43
43 #
Average number of cybersecurity tools deployed per large enterprise, most requiring their own endpoint agent. (Gartner – Top Trends in Cybersecurity for 2025)
The Agent-Dependent Architecture of Cybersecurity Products
A cornerstone of cyber security protections has been on-device agents for nearly all security functions such as file scanning, process monitoring, network traffic inspection, and behavioral analysis, all of which cannot be performed remotely and all of which require a privileged process running locally on the device. Because of this, every security vendor in every product category delivers their solution through a resident agent. A representative table shows the most common categories and their deployment model.
| Product Category | Agent Persistence |
| Endpoint Protection (EPP) | Continuous, always-on |
| Endpoint Detection and Response (EDR) | Continuous, always-on |
| Data Loss Prevention (DLP) | Continuous, always-on |
| User/Entity Behavior Analytics (UEBA) | Continuous log collection |
| Vulnerability Management (VUL) | Persistent or scan-cycle |
| Privileged Access Mgmt. (PAM) | On-session or continuous |
| IT Asset and Patch Management (ITSM) | Continuous, always-on |
| Managed Detection and Response (MDR) | Continuous telemetry sensor |
Sources: Gartner Magic Quadrant EPP 2025, Frost and Sullivan Endpoint Security 2024-2028
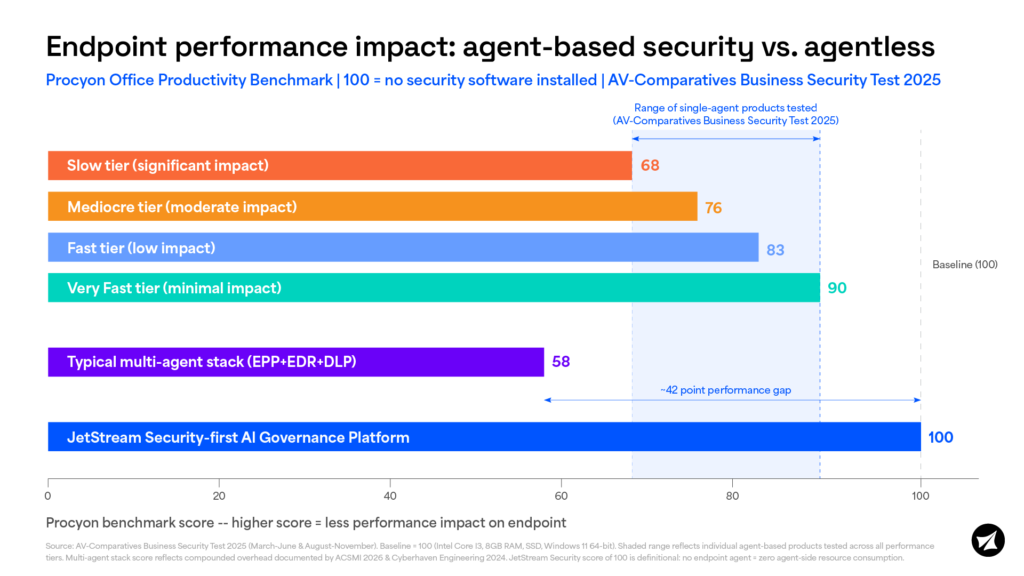
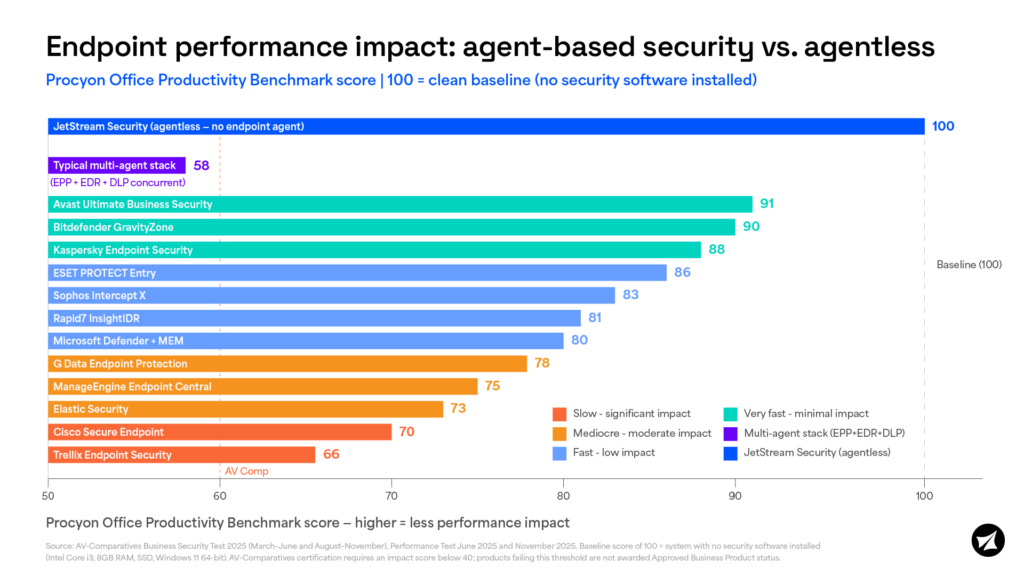
Agent Bloat: Documented Performance Impact
Agent sprawl occurs when an endpoint runs multiple independently developed security agents that compete for the same finite resources. Two distinct performance problems result. Direct impact happens when an agent intercepts a user action before allowing it to complete, such as a DLP agent inspecting a file transfer or an antivirus agent scanning a URL. The user experiences this as delay. Indirect impact happens when multiple agents consume CPU, memory, and disk I/O simultaneously, slowing the entire system regardless of what the user is doing. (Cyberhaven – Evaluating Security Agents and Their Impact on Endpoint User Productivity 2024)
ACSMI’s 2026 State of Endpoint Security report found that enterprises layering EPP, DLP, and EDR agents on the same device experienced telemetry conflicts, resource drag, and detection gaps. “63% of those firms increased security budgets in 2024, yet only 27% saw meaningful improvement”, with agent sprawl cited as a primary reason. Beyond resource competition, agents from different vendors are also documented to actively conflict at the operating system level, where two agents hooking the same kernel events can trigger each other’s detection logic and produce CPU spikes neither vendor designed nor tested for. Now the customer is left to deconflict and communicate with the users on the impacts.
“Large enterprises deploy 6-10 agents to their entire fleet. I am yet to meet a customer who wants to deploy another one. JetStream’s SAIG platform was designed to provide comprehensive visibility and control over AI assets in an organization and we are able to do so without adding the overhead of another agent.” – Raj Rajamani, Co-Founder and CEO
Supply Chain: Reduce the Attack Surface
Each security agent deployed in an enterprise environment represents an implicit, unconditional trust relationship with that vendor’s entire software development and update pipeline. Should a threat actor compromise that pipeline, the agent’s pre-existing elevated privileges on the endpoint remove the need for any further escalation, providing immediate, broad access to the systems it was designed to protect. Automatic update mechanisms, which are operationally necessary for security products to remain effective, become a silent and efficient delivery channel for malicious code across an organization’s entire endpoint fleet simultaneously. Amongst the many things the SolarWinds event demonstrated, this risk seen at scale, where a single compromised vendor update reached over 18,000 organizations, underscoring that every additional security agent an enterprise deploys is also an additional supply chain attack surface it accepts.
“Introducing yet another supply chain risk and potentially another SolarWinds event is in no-one’s best interest. The current landscape is like the “Hunger Games” of endpoint security agents and enterprises simply don’t need yet another endpoint agent to enable trust in AI” – Jared Phipps, Co-founder and COO
The AI Governance Inflection Point
Every pain point documented above—agent sprawl, resource contention, supply chain exposure—was established long before enterprises began adopting AI at scale. Now the same organizations managing 43 security tools are being asked to govern a new category of technology that touches every department, every workflow, and every data set. The question facing executive teams is not whether AI governance is necessary, but whether it can be achieved without compounding the operational burden they are already struggling to manage. JetStream’s answer is architectural: govern AI without deploying another agent.
Benefits of JetStream’s Agentless Approach
- No new attack surface. One fewer vendor pipeline with privileged access to your endpoints means one fewer supply chain risk to accept.
- Zero new agents. JetStream presents zero kernel-level contention with existing EDR, DLP, FIM, or PAM deployments.
- Zero endpoint performance impact. No CPU cycles, memory, or disk I/O consumed on managed devices
- Faster incident triage. When an end user reports “my computer is running slow,” your team has one fewer agent to rule out
- No deployment overhead. Lightweight connectors replace the FTE hours typically spent deploying, updating, and deconflicting yet another endpoint agent
At JetStream Security, we took this challenge seriously. Our agentless platform delivers enterprise security-first AI governance at scale.
Request a demo of JetStream SAIG Platform™ to see how our agentless solution and its components work together to make AI predictable, controlled, and scalable in production.

